Offensive vehicle security toolbox makes car hacking easier
The new system is designed to save security researchers time and effort spent reverse-engineering the message format of every vehicle they study.
 Enlarge
Enlarge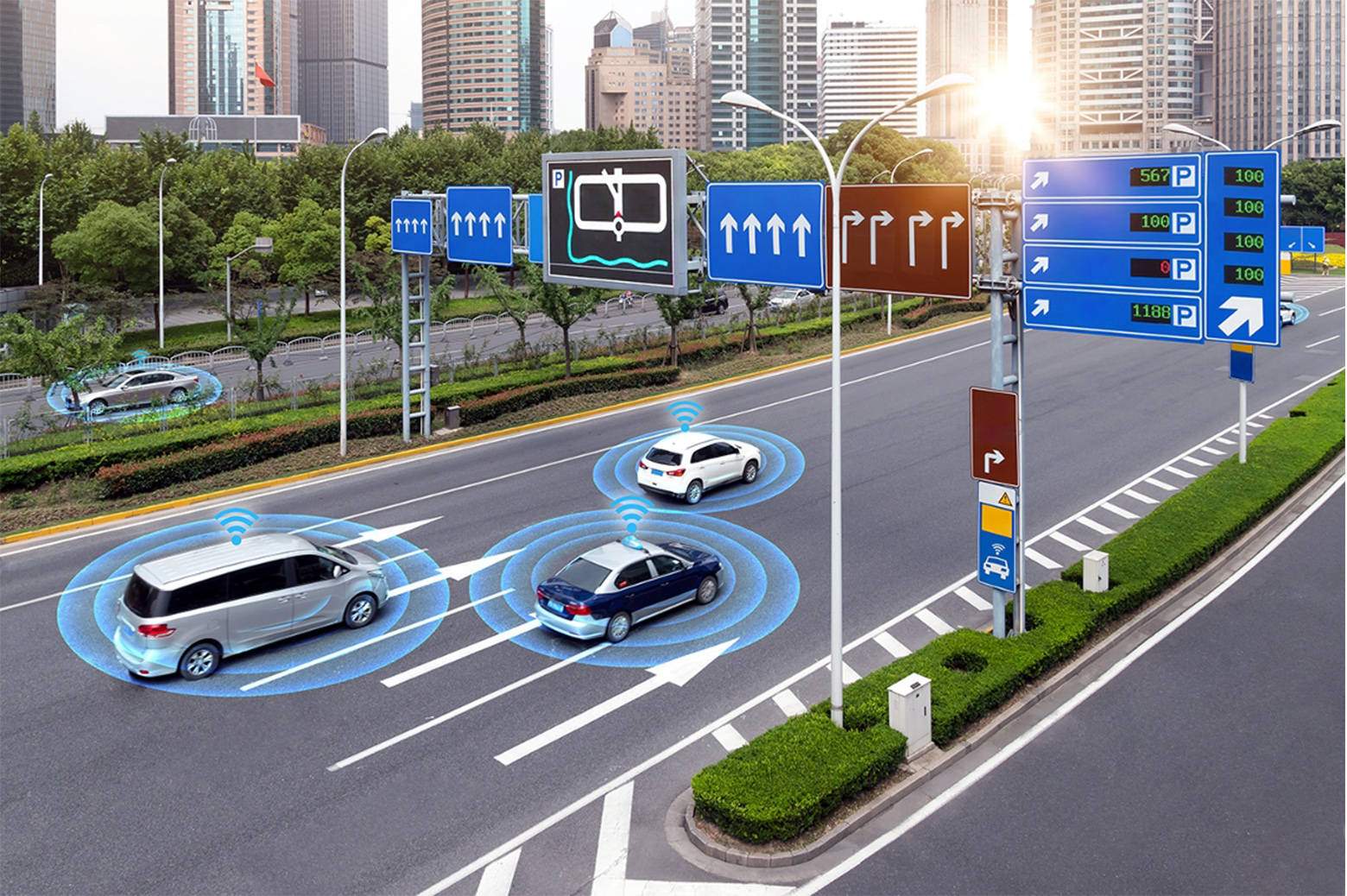
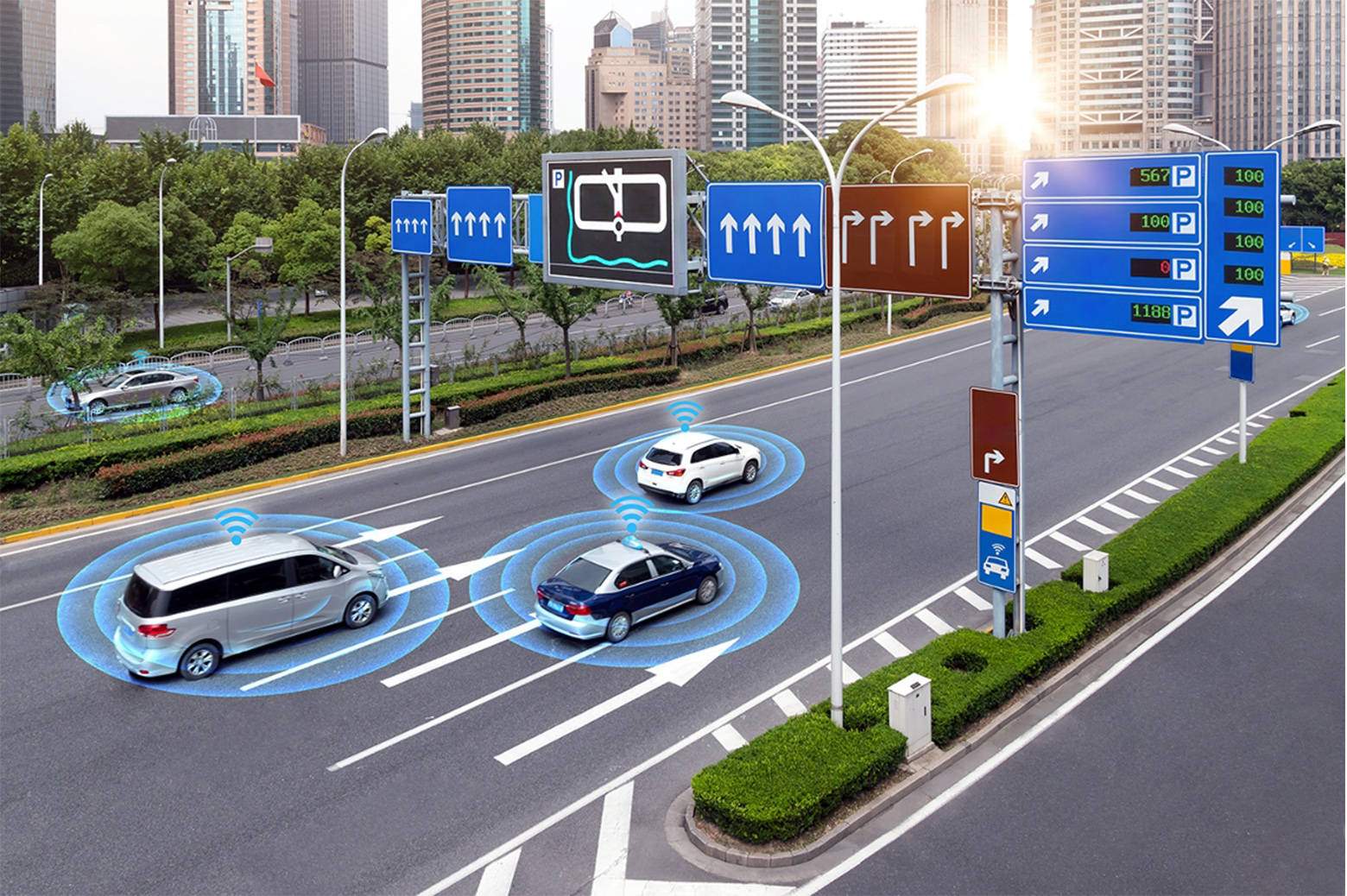
Security researchers know well that in order to fix something, you first have to figure out how to break it. This is no different in the world of modern vehicles, which come loaded down with electronics that generate and swap huge amounts of data. This is particularly true for autonomous and connected vehicles, whose components allow interaction not only with physical interfaces but also with the Internet and mobile devices.
At the heart of these systems is a robust, specialized internal communications network that connects the car’s components called a CAN bus (for Controller Area Network). This message-based protocol allows microcontrollers and devices to communicate with each others’ applications in a distributed fashion – and it also poses as the main point of weakness for security breaches.
Vehicle security attacks to date have all shared one very important feature – they all ultimately require write access to the CAN bus. But in order to do that, one has to know the message format of the CAN bus to inject meaningful data. All makes and models of vehicles have different message formats that are proprietary to the car manufacturer which hopes to prevent cybersecurity attacks on vehicles by not disclosing translation tables for CAN data. In order to cause targeted and intentional changes in vehicle behavior, malicious CAN injection attacks require knowledge of these translation tables.
Ironically, this has made researching possible attacks and designing fixes time-consuming and difficult for security researchers.
For them, a team of Michigan researchers led by PhD student Mert Pesé and Kevin and Nancy O’Connor Professor of Computer Science Kang Shin has developed LibreCAN, a system to automatically translate most CAN messages with minimal effort. The protocol is designed to save security researchers the time and effort they spend manually reverse-engineering the CAN messaging format of each vehicle they study. This makes it easier to determine how new attacks can be used against a number of makes and models at once and design necessary defenses.
Although most defensive solutions do not require knowledge of a vehicle’s message semantics, discovering the attacks in the first place ultimately does. A straightforward and automated way to reverse-engineer CAN bus data could greatly accelerate vulnerability research and allow software patches to be distributed before malicious entities become aware of vulnerabilities, according to the authors.
LibreCAN is the first such system to achieve this, allowing researchers to reverse-engineer a relatively complete CAN communication matrix for any given vehicle.
The system can generate the vehicle’s communication matrix in less than two minutes. Importantly, all three phases in the system can run and generate results without human intervention, requiring only about 40 minutes of collected driving and specific experimentation data to run accurately on a vehicle. The team produced these results with tests on four different real vehicles.
This paper, titled “LibreCAN: Automated CAN Message Translator,” will be presented at the 2019 ACM Conference on Computer and Communications Security (CCS) in London, United Kingdom.
 MENU
MENU