Two Michigan papers win top awards at IEEE Security and Privacy Symposium
One of the paper describes and demonstrates a malicious hardware backdoor. The other demonstrated security failings in a commercial smart home platform.

 Enlarge
Enlarge
Two papers authored by EECS researchers were selected for top honors at the 37th IEEE Symposium on Security and Privacy, which was held May 23-25 in San Jose.
One of the papers, describing and demonstrating a malicious hardware backdoor, received the Distinguished Paper Award. The second, which demonstrated security failings in a commercial smart home platform, received the Distinguished Practical Paper Award.
Building an Undetectable Backdoor into Silicon

 Enlarge
Enlarge
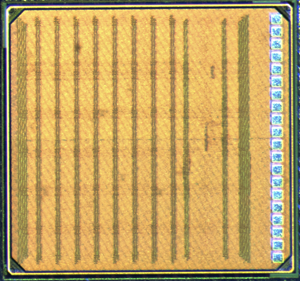
In “A2: Analog Malicious Hardware”, the authors describe a hardware backdoor that can be secretly added to a microprocessor design late in the fabrication stage, and then triggered later via software commands to trip the system’s “privilege” bit and take over control of the host system.
Unlike previous attempts to create hardware backdoors which required hundreds of gates implemented using digital logic, the researchers created a design based on a single capacitor and a few transistors wrapped-up in a single gate – a true needle in a haystack. It works by siphoning charge from a target wire every time it toggles (through the execution of an innocuous piece of computer code) and storing that charge in the capacitor. If the wire toggles infrequently, the capacitor voltage stays near zero volts due to natural charge leakage. When the wire toggles frequently, charge accumulates on the capacitor faster than it leaks away, eventually fully charging the capacitor. When the voltage on the capacitor rises above a threshold, it deploys the payload, whose output is attached to a flip-flop for they system’s privilege bit. After deploying, the capacitor is discharged, making the malicious circuit virtually invisible to post-attack testing.
 Enlarge
Enlarge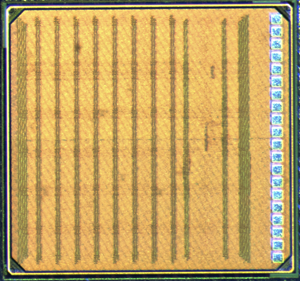
To demonstrate the attack, the researchers built an actual chip containing just such a malicious circuit. Their experiments show that it is trivial for a knowing attacker to activate the attack and escalate the privilege of their unprivileged process – all from usermode code, without operating system intervention.
The paper was authored by Michigan researchers Kaiyuan Yang, Dr. Matthew Hicks, Qing Dong, Prof. Todd Austin, and Prof. Dennis Sylvester.
Read more about the “demonically clever” silicon backdoor here.
Demonstrating Security Flaws in the SmartThings Smart Home Platform

 Enlarge
Enlarge
In “Security Analysis of Emerging Smart Home Applications”, the authors describe the first in-depth empirical security analysis of an emerging smart home programming platform, the commercially available SmartThings platform. SmartThings has the largest number of apps among currently available smart home platforms, and supports a broad range of devices including motion sensors, fire alarms, and door locks. It operates from a proprietary, closed-source cloud backend, making scrutiny challenging, but after analyzing 499 SmartThings apps and 132 device handlers, the researchers were able to detect security shortcomings.
The researchers exploited the design flaws to construct four proof-of-concept attacks that secretly planted door lock codes, stole existing door lock codes, disabled vacation mode of the home, and induced a fake fire alarm. They conclude their paper with security lessons for the design of emerging smart home programming frameworks.
The paper was authored by Michigan researchers Earlence Fernandes and Prof. Atul Prakash with Jaeyeon Jung of Microsoft Research.
 MENU
MENU 
